Network Scanning Techniques for Security Management

A comprehensive guide to network scanning techniques for effective security management, including understanding internal and external threats, using firewalls, and scanning desktops, servers, and gateways. Featuring expert insights from authors Dr. Stephen C. Hayne and Ofir Arkin.
- Uploaded on | 2 Views
-
 falko
falko
About Network Scanning Techniques for Security Management
PowerPoint presentation about 'Network Scanning Techniques for Security Management'. This presentation describes the topic on A comprehensive guide to network scanning techniques for effective security management, including understanding internal and external threats, using firewalls, and scanning desktops, servers, and gateways. Featuring expert insights from authors Dr. Stephen C. Hayne and Ofir Arkin.. The key topics included in this slideshow are . Download this presentation absolutely free.
Presentation Transcript
1. Scanning This presentation is an amalgam of presentations by Mark Michael, Randy Marchany and Ed Skoudis. I have edited and added material. Dr. Stephen C. Hayne
2. The Source! “Network Scanning Techniques – Understanding how it is done” Author: Ofir Arkin
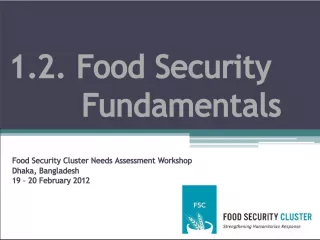
3. NETWORK SCANNING Fire Internet Gateway Web Server Mail Server Database Server Domain Controller Internal Threats External Threats wall SCANNER SCANNER Desktops
4. Intro to Intelligence Gathering Techniques 3 Major Steps Foot Printing Scanning Enumeration Similar to Military Gather information on the target Analyze weaknesses Construct and launch attack
5. Footprinting Construct a profile of the target site Adminstrative, technical & billing contacts from the ARIN database (whois utility) IP Address range DNS Servers Mail Servers Firewalls
6. Scanning Art of detecting which systems are alive and reachable on the Internet What services do they offer? TCP/UDP running on each system System architecture (Unix, Windows, etc.) OS version and patch levels
7. Enumeration The process of extracting valid accounts or exported resource names from systems Uses active connections to systems and queries, therefore, more intrusive than footprinting or scanning OS specific Gathers userid, group names, system banners, routing tables, SNMP info
8. Intro to Scanning What are scanners doing? What do they look like(signature)? How do they operate in order to accomplish their tasks? What kind of information is collected? How serious is the threat?
9. Scanning: Ping Sweeps ICMP Echo Requests(ICMP Type 8) to the target and wait for ICMP Echo Reply (ICMP Type 0) Unix Tools Fping, gping, nmap Windows Ping, pinger from Rhino9 (this is a extremely fast scanner that sends multiple ICMP echo requests concurrently Defense: block ICMP echo requests
10. Scanning: Broadcast ICMP Send ICMP Echo Request to broadcast address on the subnets Unix boxes will answer requests directed to the network so we can identify the Unix boxes using this technique Windows boxes won’t respond
11. Scanning: Non-ECHO ICMP Use non-ECHO ICMP protocols to bypass the ‘block ICMP echo’ filters ICMP type 13 (TIMESTAMP) will query a system for the current time ICMP type 17 (Address Mask Request) is used by diskless systems to obtain its subnet mask at boot time. Tools: icmpush, icmpquery
12. Scanning: TCP Sweeps TCP SYN or TCP ACK packets sent to the target network telnet, FTP, HTTP, SMTP are the common ports scanned Firewalls can spoof the response so this isn’t a reliable scanning method Tools: nmap, hping (also allows packet fragments to be sent)
13. Scanning: UDP Sweeps Relies on the ICMP PORT UNREACHABLE message which is sent by a closed UDP port If not received, the port is assumed to be open Not reliable because: Routers can drop UDP packets Many UDP services don’t respond correctly Firewalls usually drop UDP packets except DNS
14. Scanning: Port Scanning Goal: determine what services are running or in a LISTENING state The services may suffer from vulnerabilities A number of port scan techniques
15. Port Scanning TCP Connect() scan SYN packet sent to target port If SYN/ACK is received, port is active If RST/ACK is received, port is dead Finish the 3-way sequence by sending an ACK then terminate the connection Easily detected by looking at syslogs for connection or error messages
16. Port Scanning TCP Half Open Scan (SYN Scan) Send the SYN packet to the target If SYN/ACK received, the port is active If RST/ACK received, the port is dead We do NOT complete the connection
17. Advanced Port Scanning Stealth Scanning techniques Intentionally violate the 3-way handshake SYN/ACK scan FIN scan XMAS scan NULL scan RFC 793 states that closed ports must reply with a RST packet to our probe
18. Stealth Scanning SYN/ACK scan Send SYN/ACK to target (step 2 of the 3 way handshake) TCP should respond with RST because it figures this is a mistake We get a response which tells us the port is closed Open ports do not send anything
19. Stealth Scanning FIN scan Send a FIN to the target Wait for reply Open ports will respond XMAS scan Send TCP packet with all TCP flags – URG, ACK, PSH, RST, SYN, FIN set
20. Stealth Scanning Null Scanning Send TCP packet that turns off all flags The target should send a RST to all closed ports RFC 793 says this should work for every TCP implementation Windows, CISCO, BSDI, HP/UX, MVS, Irix are broken. They send RST to open ports as well. If FIN/NULL/XMAS scans show closed ports then SYN scan them to find open ports. If they match, you have one of the above systems.
21. Inverse Mapping Gather info about hosts or networks which aren’t there We make assumptions about what is there RESET Scan Routers will give information on a net even if the question doesn’t make sense Routers will report non-existent addresses No HOST UNREACHABLE or TIME EXCEEDED means the IP exists
22. Inverse Mapping Proxy Scanning/FTP Bounce Scanning Attacker.com connects to FTP server which has a world writable directory and opens a control connection Attacker can then ask the FTP server to initiate an active server data xfer process to send a file anywhere on the net. Hobbit’s paper has more details Use to scan behind a firewall
23. Port Scanning Techniques TCP Reverse Ident Scanning Ident protocol (RFC 1413) determines the owner of a TCP connection by communicating on port 113 Full TCP connection to the host Slow scan Defeats IDS that look for lots of connection in a short period of time. Typical scan rate: 2 ports/day
24. Port Scanning Techniques Fragmentation Scanning All IP packets can be fragmented RFC 791 defines the min/max fragment size 8 octets (min frag size) are enough to contain the src/dst port numbers This forces the TCP flags field into the second fragment
25. Port Scanning Techniques Fragmentation Scanning Some filters/IDS may incorrectly reassemble or completely miss portions of the scan Filters that queue all IP fragments can handle this method Fixed in most vendor’s products
26. Port Scanning Techniques Decoy Scanning The target net thinks the hosts you specify as decoys are scanning them also Makes it impossible to determine who the real scanner is Signature: TTL field usually contained the same number Nmap bypasses this error Traceroute the source IP
27. Port Scanning Techniques Coordinated Scans Multiple IP’s used in the scan Each one of them probes specific ports in a different time period, different scan rate Detection depends on the time period the probes take place Coordinated scans are the most discrete way of probing a target
28. Operating System Detection Banner Grabbing Telnet banners identify the OS version FTP/IIS SYST command DNS HINFO Record Pair of strings identifying the host’s HW
29. Operating System Detection TCP/IP/Stack Fingerprinting Uses distinct variation in TCP stack implementation to get the OS type Send specific TCP packets to target and observe the response Varies with vendor because they interpret the RFC differently when they wrote their TCP stacks
30. Operating System Detection FIN packet sent to open port. RFC 793 says “don’t respond to the FIN”. Many stacks will respond with a RST. Windows, BSDI, CISCO, HPUX, MVS, Irix do this.
31. Operating System Detection Bogus Flag Probe SYN packet with undefined flag is sent Linux < 2.0.35 will keep the flag in their response. Other OS will RST the connection TCP ISN sampling Find pattern of the ISN Traditional 64K (older Unix) Random Increment (FreeBSD, DGUX, Irix, newer Solaris) True Random (linux) Time Dependent Modules (MS Windows)
32. Operating System Detection Don’t Fragment Bit Some OS use this bit to enhance performance TCP Initial Window Some OS stack implementations have a unique initial window size on their returned packets AIX returns Ox3F25, OpenBSD, FreeBSD use 0x402E
33. Operating System Detection ACK Value Some IP stacks differ in the value they use for the ACK field Send FIN/PSH/URG to a closed port. Most implementation will set the ACK number in the returned packet to be the same as the sequence number received. Windows responds with ACK=Sqn#+1
34. Operating System Detection ICMP Error Message Quenching RFC 1812 suggests limits on various error message rates. Only a few OS follow the RFC. Send UDP packets to random, high, UDP port and count the number of unreachable messages received within a given amount of time.
35. Operating System Detection ICMP Message Quoting ICMP error messages should quote a small amount of info from the ICMP message that caused the error. Example: Host unreachable This is quoted when the PORT UNREACHABLE message is received in the IP Header + 8 bytes. Solaris and Linux provide more info than is needed
36. Operating System Detection ICMP Error Message Echoing Integrity Some OS stack implementations alter the IP header when sending back an ICMP error message. Another way to target an OS. ICMP Type of Service ICMP PORT UNREACHABLE TOS field Linux uses 0xC0 for this value. All others use 0.
37. Operating System Detection Fragmentation Handling Different stack implementations handle overlapping fragments differently. TCP Options RFC 793, RFC 1323 define TCP options. Not all OS implement host options. Send query with option set. Target sets the option only if it supports it. Some OS support advanced options, others don’t.
38. Banner Checks Check the service output retrieved during TCP port scan for version number 220 mail.domain.com ESMTP Sendmail 8.6.1/8.6.1 , the version number indicates a vulnerability. Banner checks cannot always determine whether a vulnerability has been patched Vulnerabilities that can be detected by banner checks include: – SMTP ( Sendmail, MMDF, Lotus Domino, etc.) – POP/IMAP – FTP ( wu-ftpd, etc.) – SSH – INN
39. URL CHECKS Check for vulnerabilities in specific programs on web server: You can try to exploit the vulnerability: Check whether specially crafted URL returns contents of some file which is known to reside on the server. Or just see if the file exists on the web server: Check whether URL returns 200 OK response.
40. Firewalking A technique used to gather information about a remote network protected by a firewall. 2 purposes Determine the ACL of a FW by mapping open ports on the FW. If FW drops ICMP ECHO request/reply, this technique is effective
41. Firewalking Uses traceroute style packet filtering to determine whether the packet passes through the FW. Need 2 pieces of info IP of last known gateway BEFORE the FW. This is our waypoint. IP of host located behind the firewall.This is used as a destination to direct packet flow.
42. Firewalking If we traceroute a host behind the FW and get blocked by the ACL, we find the FW. We then try to traceroute same host using different transport protocol (TCP, UDP, ICMP). If we get a response, 2 possible conclusions: This particular traffic is allowed by the FW. We know a host exists behind the FW. Trying to pass packets on all ports/protocols through the FW, monitor the response will produce the ACL. Use slow scan to avoid detection! Send packets to all hosts inside the net.
43. War Driving With a laptop and wireless card, an attacker can drive down the street and join many wireless LANs! Windows Tools: NetStumbler WinPcap Linux Tools: Airsnort WEPCrack More here
44. War Chalking Variant of “hobo” language Key: SSID () – closed, )(– open Bandwidth Retina )( 1.5
45. War Driving Defenses Use Virtual Private Network (VPN) All data from end system to VPN gateway inside of wireless device encrypted and authenticated SLAN is a freeware VPN on Linux or Windows: http://slan.sourceforge.net Allow connection to specific MACs
46. Conclusions Understanding the importance of detecting these scans could prevent intrusions to the scanned systems. Use an IDS to gather scan signatures. Develop filters for these scans