Exploring the Fundamentals of Cryptography

Cryptography involves securing communication from third-party adversaries using math, computer science, and electrical engineering. The Serpent Cipher system uses algorithms to transform information while symmetric and asymmetric cryptography differ in their encryption techniques. In the past, cryptography was all about turning information to nonsense using decoding keys.
- Uploaded on | 6 Views
-
 vincenzo
vincenzo
About Exploring the Fundamentals of Cryptography
PowerPoint presentation about 'Exploring the Fundamentals of Cryptography'. This presentation describes the topic on Cryptography involves securing communication from third-party adversaries using math, computer science, and electrical engineering. The Serpent Cipher system uses algorithms to transform information while symmetric and asymmetric cryptography differ in their encryption techniques. In the past, cryptography was all about turning information to nonsense using decoding keys.. The key topics included in this slideshow are . Download this presentation absolutely free.
Presentation Transcript
2. the basics • cryptography deals with techniques for secure communication in the presence of third parties (adversaries). • modern cryptography uses mathematics, computer science, and electrical engineering • the word “cryptography” originates from two Greek words: “hidden/secret” and “writing”
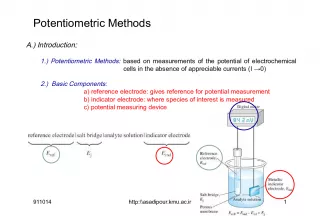
3. serpent cipher systems • a cipher is the algorithm that transforms information symmetric vs. asymmetric
4. the olden days • cryptography was basically encryption information -> nonsense -> information • whoever wrote the message provided the recipient with the decoding key
5. exhaustive key search on a Caesar Cipher code = XMZVH
6. modular arithmetic in a Caesar Cipher, a shift of 26 is the same as a shift of 0. for example: 37 = 11(mod 26)
7. we want a large number of keys (but having lots of keys is no guarantee of a strong system) number of potential keys = number of ways 26 letters can be arranged 26! = 403,291,461,126,605,635,584,00 0,000
8. Mary, Queen of Scots 1542 - 1587 German Armed Forces, WWII Enigma Machine a large number of keys does not guarantee that a cipher is unbreakable
9. Diffie-Hellman Key Exchange
10. asymmetric cipher systems and more modular arithmetic
11. the primitive root of 17 is a number that has no factors in common (3)